Some malware from my Honeypot

So I've been running my HoneyPot for many months now, and I do analysis on some samples from time to time. Following are 2 interesting scripts.
While one is clearly a tool to demonstrate an attack, now being used in the wild, the other one is a simple port scanner with basic dictionary password attack.
There are a lot of small things that can be noticed including dictionary, agents, ports scanned, how the payload is being created etc. While very basic, they do provide an insight on some very basic security measures. But it also highlights that many of the attacks are nothing but basic script junkies from some random compromised hosts.
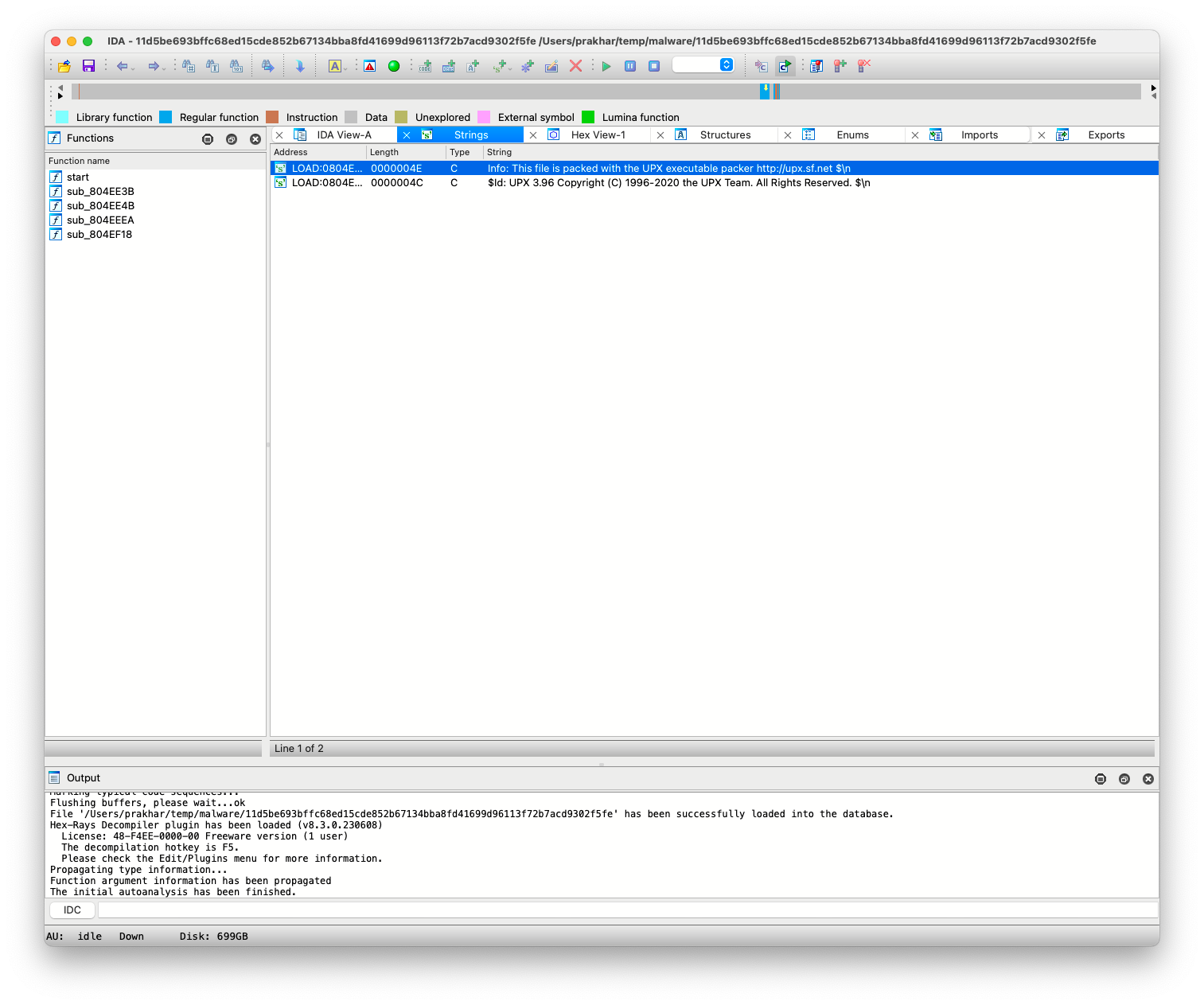
Most malwares also hide thier contents, by making a self-extracting archive, like the following one. In fact, UPX is quite common for this:
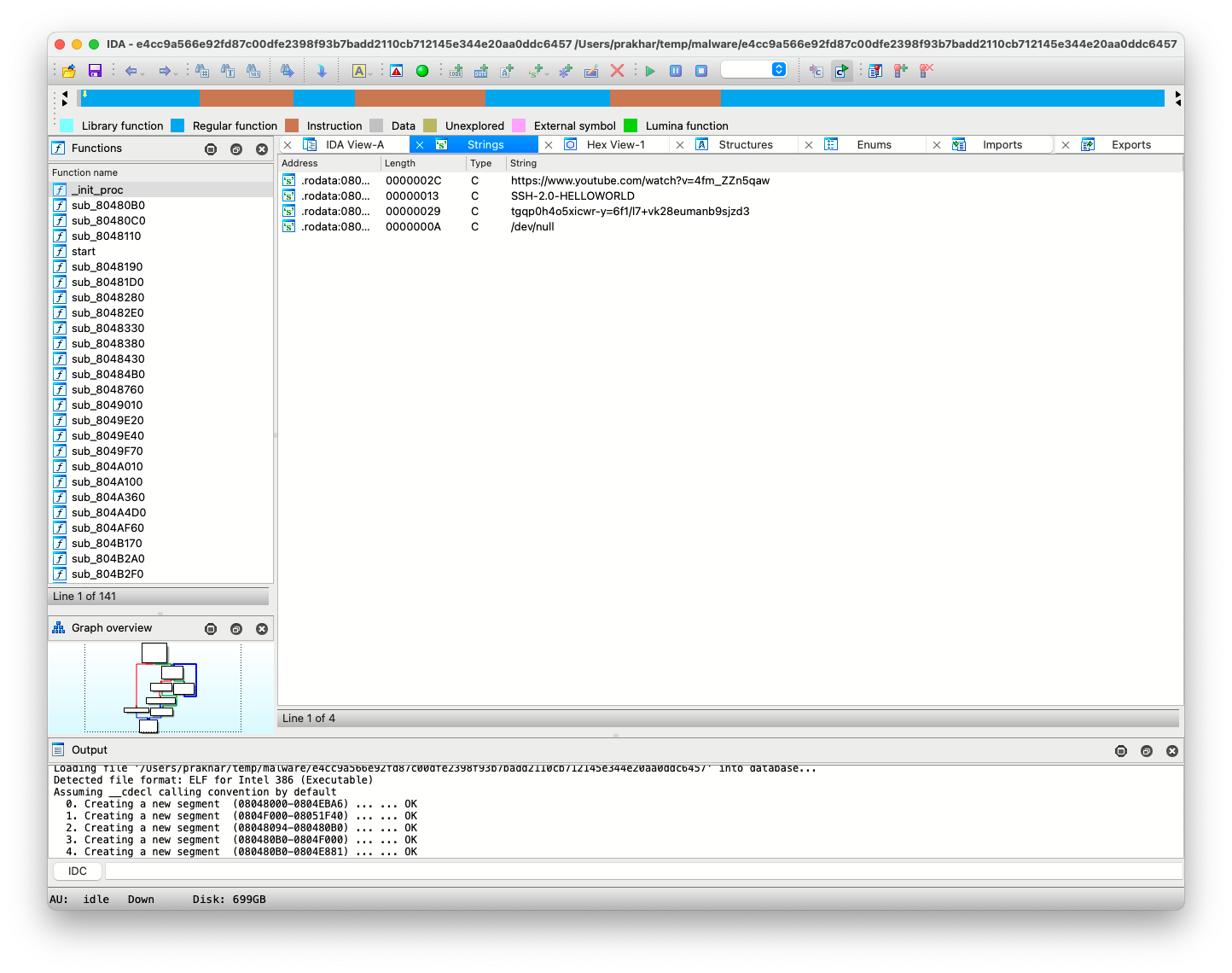
Then there are some which try to DDoS using our HoneyPot as a node of the botnet. But some go further to increase watch count of the video!
It is interesting to see these samples and I'll try to dive deeper in future.